Mimikatz-Centric Timeline Snippet
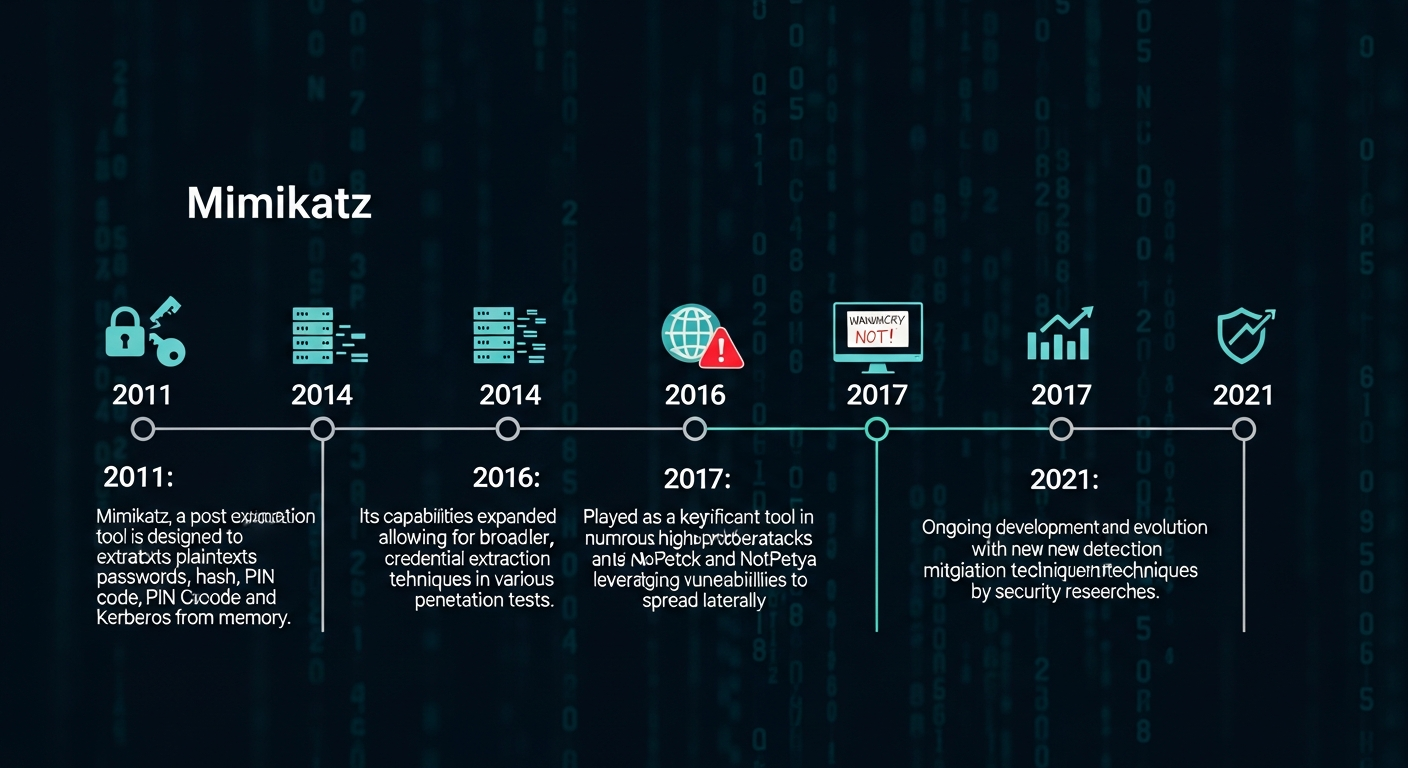
In the world of cybersecurity, understanding attack tools and techniques is crucial. One tool that often pops up is Mimikatz, famous for its ability to extract credentials and help security professionals test systems. But what is a mimikatz-centric timeline snippet, and why does it matter? Simply put, it’s a chronological snippet or log focusing on Mimikatz activities during a security investigation.
This article will break down everything you need to know about mimikatz-centric timeline snippets, how they’re used in real scenarios, and why they are valuable for incident response. Whether you’re a beginner in cybersecurity or a seasoned professional, this guide is designed in simple terms, easy to understand, and fully actionable.
What is a Mimikatz-Centric Timeline Snippet?
A mimikatz-centric timeline snippet is a focused log that highlights Mimikatz-related events. These snippets can include authentication attempts, credential dumps, or system changes made by attackers using Mimikatz.
Think of it as a timeline that shows when and where Mimikatz acted on a system. Analysts use these snippets to trace attacks, identify compromised accounts, and prevent future breaches. Instead of scrolling through hundreds of system logs, a focused snippet allows quick detection of malicious activity.
How Mimikatz Works
Mimikatz is a tool used to extract passwords and authentication tokens from Windows systems. It works by reading memory where credentials are stored. While attackers misuse it, security experts also use it for testing and strengthening defenses.
The beauty of a mimikatz-centric timeline snippet is that it isolates Mimikatz’s impact. By tracking only relevant events, teams can clearly see what happened, when it happened, and who may be affected.
Importance of Mimikatz-Centric Timeline Snippets
Focusing on Mimikatz activity saves time during investigations. Without it, security analysts might miss key events hidden in generic logs.
These snippets also help in compliance audits. Organizations can prove they monitored credential attacks effectively. A mimikatz-centric timeline snippet serves as both a detection tool and a reporting aid for cybersecurity teams.
Key Components of a Timeline Snippet
A good timeline snippet includes:
- Timestamp – Exact date and time of activity
- User Account – Which account was targeted
- Event Type – Login attempt, password dump, or privilege escalation
- Source – Machine or IP where Mimikatz ran
- Impact – What data or systems were compromised
By including these details, snippets provide a clear and actionable overview.
Creating a Mimikatz-Centric Timeline Snippet
To create a snippet, you first collect logs from Windows Event Viewer, Sysmon, or SIEM tools. Filter events related to credential access or unusual system modifications. Then, organize them chronologically to form a readable snippet.
Security teams can even automate this using scripts. This ensures that every time Mimikatz is detected, a mimikatz-centric timeline snippet is automatically generated, saving hours of manual work.
Real-World Example
Imagine a company notices suspicious logins. Analysts check the mimikatz-centric timeline snippet and see that an admin account was accessed via Mimikatz at 2:30 AM. Because the snippet isolates these events, they quickly identify the breach source, revoke compromised credentials, and prevent further damage.
Benefits for Security Professionals
- Faster Detection: Identify attacks in minutes, not hours.
- Clear Evidence: Shows exact actions taken by attackers.
- Better Reporting: Simplifies sharing findings with managers.
- Preventive Measures: Helps strengthen weak spots in systems.
Common Challenges
While timeline snippets are helpful, they aren’t perfect:
- Incomplete Logs: If logging isn’t enabled, snippets miss events.
- False Positives: Not every suspicious activity is malicious.
- Data Overload: Large networks generate many events, requiring filtering.
Despite challenges, using a mimikatz-centric timeline snippet drastically improves response efficiency.
Best Practices
- Enable detailed logging in all systems.
- Regularly update detection scripts.
- Combine snippets with SIEM dashboards.
- Educate teams about Mimikatz behavior.
- Store snippets securely for audits.
Tools to Help
Popular tools that assist with generating mimikatz-centric timeline snippets include:
- Sysmon – Tracks process creation and credential access
- ELK Stack – Helps visualize timeline data
- SIEM Platforms – Automates snippet creation and alerting
Using the right tools ensures snippets are accurate, readable, and actionable.
How to Interpret Snippets
Reading a mimikatz-centric timeline snippet requires practice. Focus on:
- Repeated access attempts
- Privileged account use
- Suspicious login times
- Unusual process activity
These clues often reveal attackers’ movements within the system.
Conclusion
A mimikatz-centric timeline snippet is an essential tool for cybersecurity teams. It helps detect attacks, respond quickly, and provide clear evidence for audits. By understanding how to create, read, and use these snippets, organizations can strengthen their security posture and protect sensitive data.
If you’re serious about cybersecurity, start incorporating timeline snippets into your monitoring process today. They transform complex logs into clear, actionable insights.
FAQs
1. What is a Mimikatz-centric timeline snippet?
It’s a focused log highlighting Mimikatz activity on a system, useful for tracking credential attacks.
2. Who uses Mimikatz-centric timeline snippets?
Primarily security analysts, incident responders, and ethical hackers use them for investigations.
3. Can attackers see these snippets?
No, snippets are created internally from system logs and are only visible to security teams.
4. How do I create a snippet?
Collect logs from Windows Event Viewer or SIEM, filter Mimikatz-related events, and arrange them chronologically.
5. Why are they important?
They allow faster detection of breaches, clear reporting, and improved system protection.
6. Are there tools to automate snippets?
Yes, tools like Sysmon, SIEM platforms, and ELK Stack can automate snippet creation and alerting.